What is DKIM?
DomainKeys Identified Mail (DKIM) is an email security standard that ensures messages are not modified while travelling between the recipient and sending servers. DKIM permits organizations to take responsibility for transmitting a message in a way a recipient can verify.
The organization can be the originating website, intermediary, etc. Their domain reputation is the basis for evaluating whether or not to trust the message for delivery.
When an email arrives at the recipient's server, the server checks for a DKIM signature in the email header field. It then uses the publicly available key from the sender's DNS to verify the signature.
It helps ensure that parts of the message haven't been altered during its journey from the sender to the recipient's server.
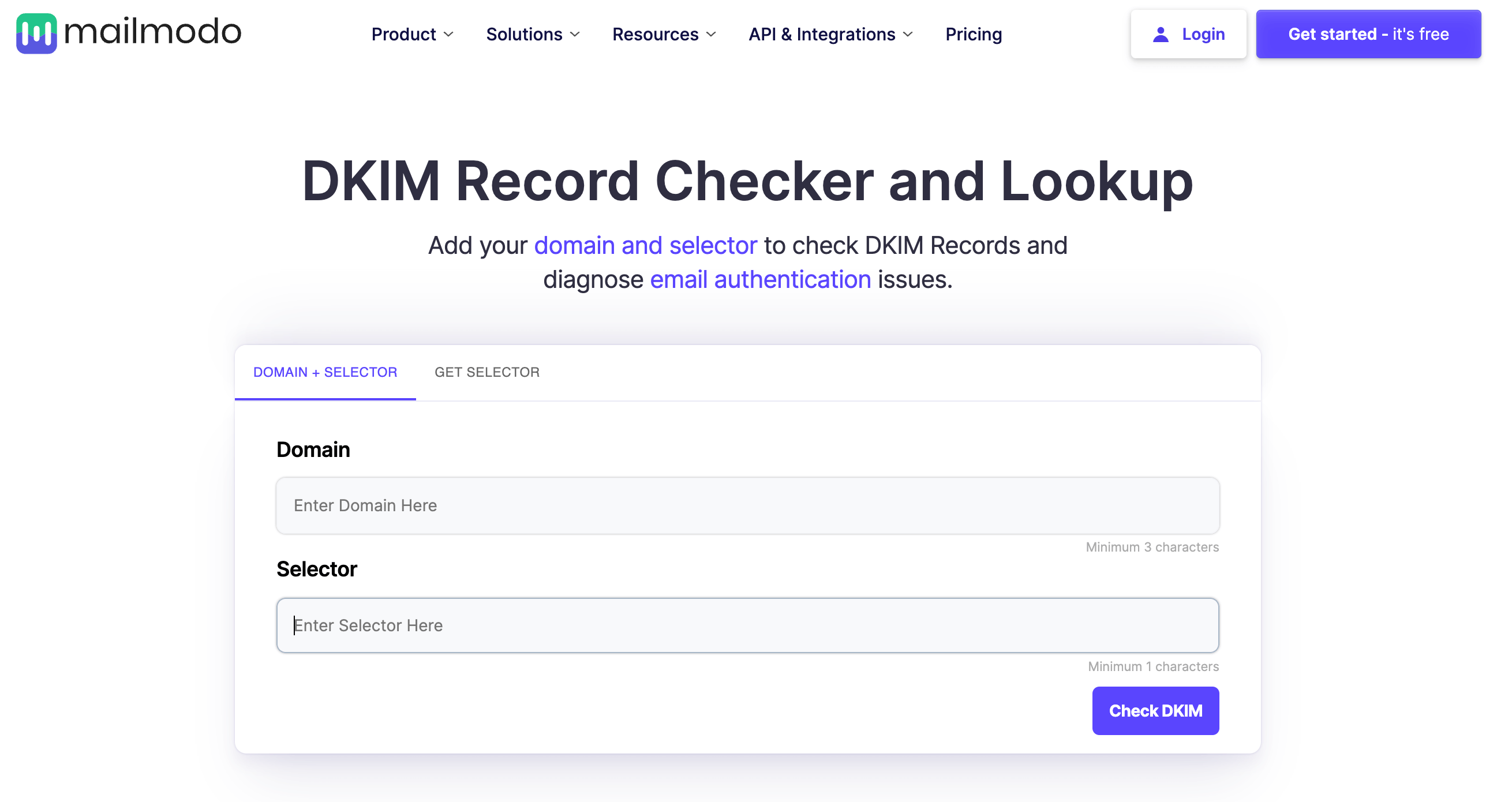
Free Tool:
Use free DKIM Checker to verify DKIM records, ensuring correct configuration, syntax, and alignment of public and private keys for email authentication.
What is a DKIM signature?
DKIM gives emails a signature header that is added to the email and secured with encryption. Each DKIM signature contains all the information needed for an email server to verify that the signature is accurate, and a pair of DKIM keys encrypt it.
The signature looks something like this:
DKIM-Signature: v=1; a=rsa-sha256; q=dns/txt; c=relaxed/simple; s=mpd3pejeeqmlqs7ztigzi2y23flpbcyg; d=mailmodo.com; t=1660826081; i=@email.mailmodo.com; h=Content-Type:List-Unsubscribe:From:To:Reply-To:Subject:Message-ID:Date:MIME-Version; bh=FBdoN7RR/uuaFsk9yZaueugs8lII6HyF3+PDrHFBgtM=; b=GOl88uQNxDM2iCkM5bQPPI8rasQr08GlNDZ8A+hJxHDKrWoJWw4xYGZRNR8+ko6L rDp
The originating email server has the "private DKIM key," which can be verified by the recipient email services or ISP with the other half of the keypair, called the "public DKIM key."
These signatures travel with the emails and are verified along the way by the email servers that move the emails toward their final destination.
Why should you authenticate emails with DKIM?
DKIM is among the top three must-have authentication protocols, and that's for good reason, as it impacts the deliverability and reputation of your domain.
Some of the reasons behind getting your domain DKIM authenticated are as follows:
Prevents sender impersonation
In the absence of DKIM, hackers can easily forge your email address and send malicious emails that appear to come from you. DKIM acts like a digital security shield, verifying the sender's identity and preventing email spoofing. This protects your brand reputation and safeguards your users from phishing attacks.
Protects your domain reputation
DKIM prevents spam emails from being sent via your domain. When DKIM signing authenticates your emails, every outgoing message will hold the DKIM signature. This message's signature will ensure that the email content is not tampered with.
Lands you in the good books of ISPs
Email service providers (ESPs) and Internet Service Providers (ISPs) rely on various measures to ensure email security. DKIM is a critical factor in their evaluation. Having a valid DKIM signature portrays you as a legitimate and trusted sender.
The better your sender's reputation will be, the more you'll land in the recipient's inbox, leading to higher deliverability.
Demonstrates commitment to security
Implementing DKIM showcases your dedication to secure email communication. This transparency fosters trust with your audience and assures them that you prioritize their safety. DKIM-authenticated emails appear more professional and reliable, leading to better engagement and response rates.
How does DKIM work
 DKIM is added as a signature to your email headers once it's verified by both the sender and receiver's server.
DKIM is added as a signature to your email headers once it's verified by both the sender and receiver's server.
The signature is verified using a private and public cryptographic key. The private key is safe and hosted on your server or your ESPs. As it's private, only you can have access to it.
To validate the DKIM signature, ISPs look at the public key hosted on your organization's DNS record. This record is public and can be accessed by anyone to verify the legitimacy of your sender's domain.
The process looks like this:
A domain owner publishes a cryptographic public key as a specially-formatted TXT record in the domain's overall DNS records.
1. On the sender's server end:
When an email is sent, the domain generates a private key. This key contains all the information the mail server needs to verify your messages.
2. On the receiver's server end:
When the recipient server receives a DKIM-signed email, it utilizes the public key published to DNS to check the source message and the message body. It is done to check if any changes were made during the transit.
Once the recipient server verifies the signature with the public key, the message is deemed authentic. After that, it is passed on to the ESP.
3. Verification of DKIM signed messages:
For any email, the signature from DKIM is like a tamper-proof seal. The signature shows that it has come from the original domain and hasn't been tampered with. Every email sent is attached with a signature, which is specially configured by the email servers to use the DKIM.
What is a DKIM record?
When an email is sent, there may be an intervention in the pipeline by a hacker. This may result in the email content getting forged. So, to address this issue, anti-spam bodies have conceptualized the DKIM record.
This happens with the help of a simple encoding and decoding method as follows:
Sender level
The email combines with a private key available at the sender server software to form an email signature. This signature is sent to the recipient along with the actual message.
Recipient level
There's a Domain Name System (DNS) record published in the world, available as the public key. The DNS record looks as follows:
m1._domainkey.yourdomain.com | TXT | v=DKIM1\; p=MIGfMA0GCSqGSIb3DQEBAQUAA4GNADCBiQKBgQDPtW5iwpXVPiH5FzJ7Nrl8USzuY9zqqzjE0D1r04xDN6qwziDnmgcFNNfMewVKN2D1O+2J9N14hRprzByFwfQW76yojh54Xu3uSbQ3JP0A7k8o8GutRF8zbFUA8n0ZH2y0cIEjMliXY4W4LwPA7m4q0ObmvSjhd63O9d8z1XkUBwIDAQAB
In the above example, "v" is the DKIM version, and "p" is the public key. This public key encodes the email signature, and the incoming email is compared with the decoded email. If the two match, that indicates the email hasn't been tampered with.
Note: If DKIM isn't passed, no authoritative action is taken. The email will still get delivered. But, if DKIM fails, the deliverability still gets impacted as ISPs might take it as a negative signal and land your emails in the junk folder.
How to set up your own DKIM key
Here's what you need to do to set up your own DKIM key with DNS configuration.
The signee must add the code in the appropriate agent to perform signing, and they ought to modify their DNS administrative tools to allow the creation of DKIM key records.
A validator must add the code to the appropriate agent and then feed the result into the portion of their system needing it, like a filtering engine.
A valid signature doesn't imply that the mail is acceptable for delivery. Acceptability requires an assessment phase. Therefore, signature validation results are fed into a vetting mechanism, which is a part of the validator's filter.
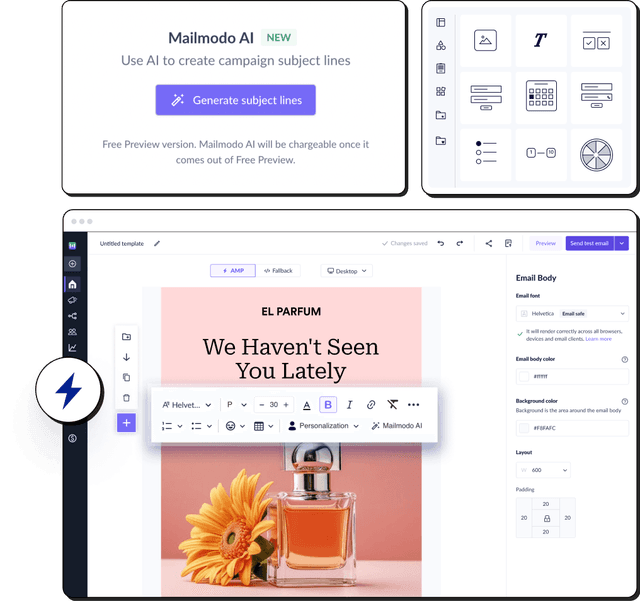
DKIM for AMP email approval from email clients
If you want to reap the benefits of sending out interactive AMP emails, you will have to get whitelisted with Yahoo Mail, Gmail, and Mail.ru, which support AMP emails.
For a successful whitelisting of your sender address, these email clients require DKIM.
How do DKIM, DMARC and SPF work together?
Email security is crucial, and DKIM, SPF, and DMARC are three protocols that work together to fight email fraud and ensure your emails reach the intended inbox. Here's a breakdown of their roles:
- DKIM (DomainKeys Identified Mail): DKIM acts like a digital signature for your emails. It adds a special code to the email header that verifies the sender's identity and checks if the message content has been altered during transit.
Think of it like a tamper-evident seal on a package.
- SPF (Sender Policy Framework): SPF creates an authorized list of email servers allowed to send emails on behalf of a specific domain. This helps prevent email spoofing, where someone forges the sender's address to make it appear from a trusted source.
Think of it like a doorman checking IDs – only authorized servers can send emails for that domain.
- DMARC (Domain-based Message Authentication, Reporting & Conformance): DMARC relies on DKIM and SPF to tell email providers what to do with emails that fail authentication. DMARC gives domain owners more control over how unauthenticated emails are handled (e.g., quarantine or reject).
Think of it like final instructions – DMARC tells email providers what action to take if an email fails the DKIM or SPF check.
Working together:
While each protocol plays a specific role, they work together for better email security:
DKIM verifies the sender and checks for tampering.
SPF verifies if the sending server is authorized for that domain.
DMARC instructs email providers on how to handle unauthenticated emails based on DKIM and SPF results.

By implementing all three protocols, you significantly enhance email security, protect your domain reputation, and ensure legitimate emails reach inboxes.
Common DKIM issues
Implementing DKIM (DomainKeys Identified Mail) can significantly enhance email security, but with its challenges. Here’s a look at some common issues that arise with DKIM and how to troubleshoot them effectively.
Problem 1: Incorrect DNS configuration
DKIM records are not found or are incorrect, resulting in failed DKIM checks.
Troubleshooting tips:
Verify DNS records: Ensure that the DKIM TXT record is properly configured in your DNS settings. The record should be a TXT type and have the correct syntax, including the correct domain selector (s=) and public key (p=). Use tools like online DNS checkers or command-line tools like dig to verify the presence and correctness of the DKIM record.
Check for propagation: DNS changes can take time to propagate. If you’ve recently updated or added DKIM records, it might take some time for the changes to be visible. Check the TTL (Time to Live) value in your DNS settings and wait for the appropriate duration.
Ensure correct domain and selector: Confirm that the DKIM selector in your DNS record matches the selector used in the email's DKIM signature. The selector is a part of the DKIM-Signature header (s=) and should match the TXT record's name in DNS.
Look for typos: Verify that there are no typos or formatting errors in the DKIM record. Common errors include missing semicolons, misplaced quotation marks, or incorrect key lengths.
DNS TXT record limits: Ensure that the DKIM record does not exceed DNS TXT record size limits. Some DNS providers might truncate long records, which can cause verification issues.
Problem 2: DKIM signature mismatch
The DKIM signature does not match, indicating potential tampering or misconfiguration.
Troubleshooting tips:
Check DKIM header fields: Ensure that the DKIM-Signature header in the email matches the fields used in your DKIM record. The header should include the correct values for h= (signed headers) and b= (signature).
Verify consistent canonicalization: DKIM uses canonicalization algorithms to prepare email content for signing. Ensure that the canonicalization settings (c=) used for signing the email match those used for verification. Mismatched canonicalization can lead to signature mismatches.
Inspect email modifications: Any changes to the email after it is signed (e.g., modifications by intermediaries) can cause signature mismatches. Ensure that no content or header fields are altered during transit.
Check for encoding issues: Ensure that there are no issues with encoding in the email. DKIM signatures are sensitive to changes in encoding, so the signature may not validate if the email content is altered.
Review key usage: Confirm that the correct DKIM private key is used for signing and that it matches the public key in the DNS record. A mismatch can result in signature verification failures.
Problem 3: Key rotation issues
DKIM keys are rotated, and the new keys are not correctly updated in DNS, leading to verification failures.
Troubleshooting tips:
Update DNS records promptly: When rotating DKIM keys, ensure that the DNS records are updated promptly with the new public key. Keep the old keys active in DNS until the new keys have propagated.
Coordinate key changes: Implement a coordinated key rotation strategy to minimize downtime. Update the DNS record with the new key and ensure that the email servers are using the updated key for signing.
Communicate key changes: Notify any partners, email service providers, or internal teams of the key rotation to ensure they are aware of the change and can update their configurations if necessary.
Verify key deployment: After key rotation, verify that the new DKIM keys are correctly deployed and operational. Test the DKIM signatures of outgoing emails to ensure that they are correctly signed and validated.
Monitor for issues: Use monitoring tools to track DKIM authentication results and detect any issues related to key rotation. This can help quickly identify and resolve problems.
Is Mailmodo compatible with DKIM authentication?
Yes, Mailmodo is compatible with DKIM. Our email specialists team helps you understand the importance of security certifications and build your IP & domain reputation for high email deliverability.
We help our users set up DKIM without any hassle to help them get whitelisted for AMP email from email clients.
Final takeaway
Security certifications increase your sender's reputation and provide you with better email deliverability. But, DKIM alone doesn't alone help you achieve that. Other authentication protocols, such as SPF, DMARC, and BIMI, are also required to leave a great impression on the ISPs.
To help you, we have written a complete guide on email authentication protocols. Go check it out and make your emails spoofing-free.


 DKIM is added as a signature to your
DKIM is added as a signature to your