What is email authentication?
Email authentication refers to the process of verifying the legitimacy of an email. It uses a set of protocols and techniques to ensure the email is coming from a claimed sender and has not been tampered with during transit.
It helps prevent cyber threats like email phishing, spoofing, and other fraudulent activities by validating the authenticity of an email’s origin.
Key benefits of email authentication
Email authentication protocols offer a robust solution to issues like spoofing and phishing, which threaten users and brands. Below, we explore the key benefits of email authentication and why it is essential for any organization looking to enhance its email security strategy:
Prevents email spoofing
Email authentication ensures that emails claiming to be from your domain are genuinely from your domain. Protocols such as DKIM and SPF prevent email spoofing by specifying mail servers that are authorized to send emails to your domain.
Improves deliverability
The sender's email addresses that are authenticated are more likely to be delivered to recipients’ inboxes rather than being sent to the spam folder, thus increasing your email deliverability.
Protects brand reputation
Email authentication standards prevent malicious people from using your given domain to send fraudulent emails. This safeguards your brand reputation by ensuring your domain is not associated with spam or phishing attacks.
Enhances security
By making it hard for spammers to impersonate your domain or email address, email authentication reduces the risk of unauthenticated messages, phishing attacks, and other email-based threats.
Email authentication protocols
The main email authentication protocols include SPF (Sender Policy Framework), DKIM (DomainKeys Identified Mail), DMARC (Domain-based Message Authentication, Reporting & Conformance), and BIMI (Brand Indicators for Message Identification). Let’s go over each of these methods in more detail:
SPF
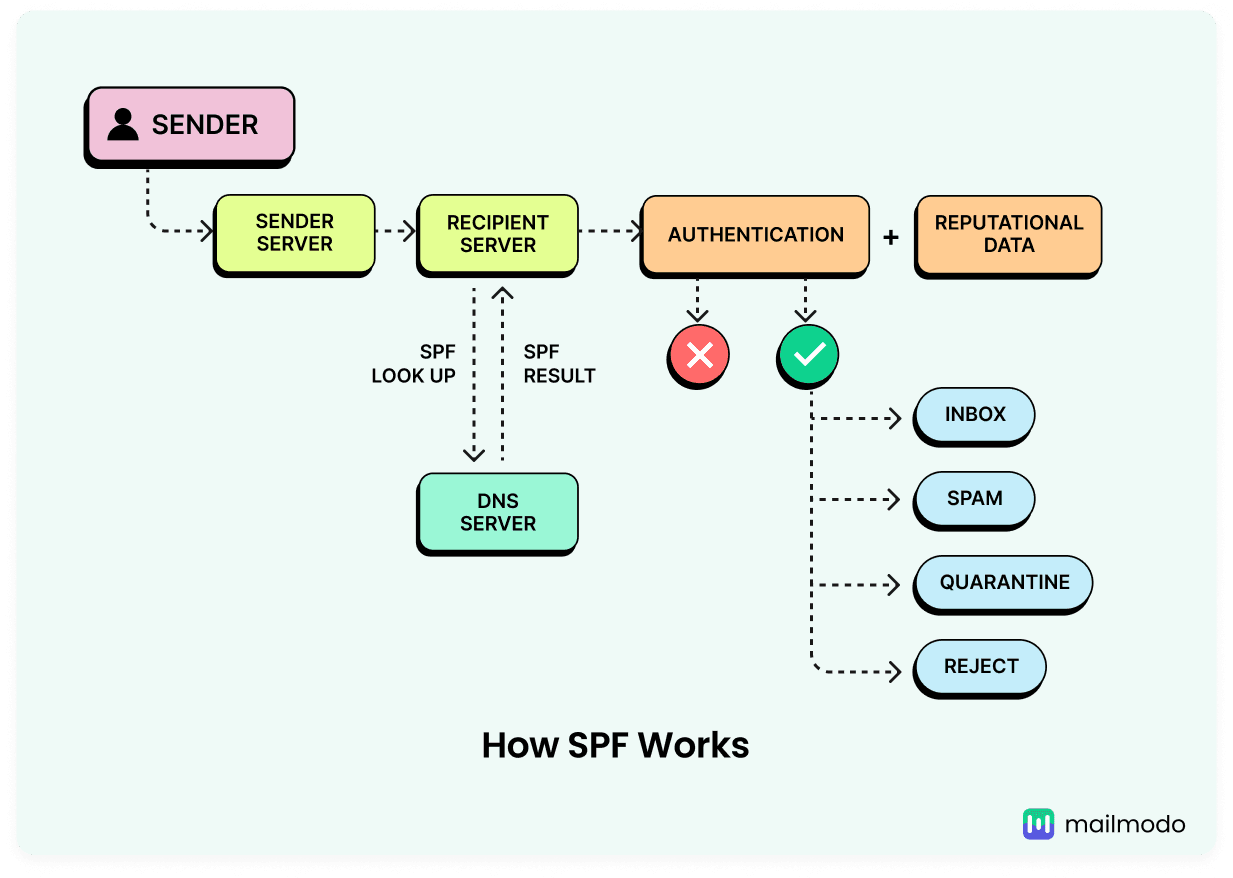
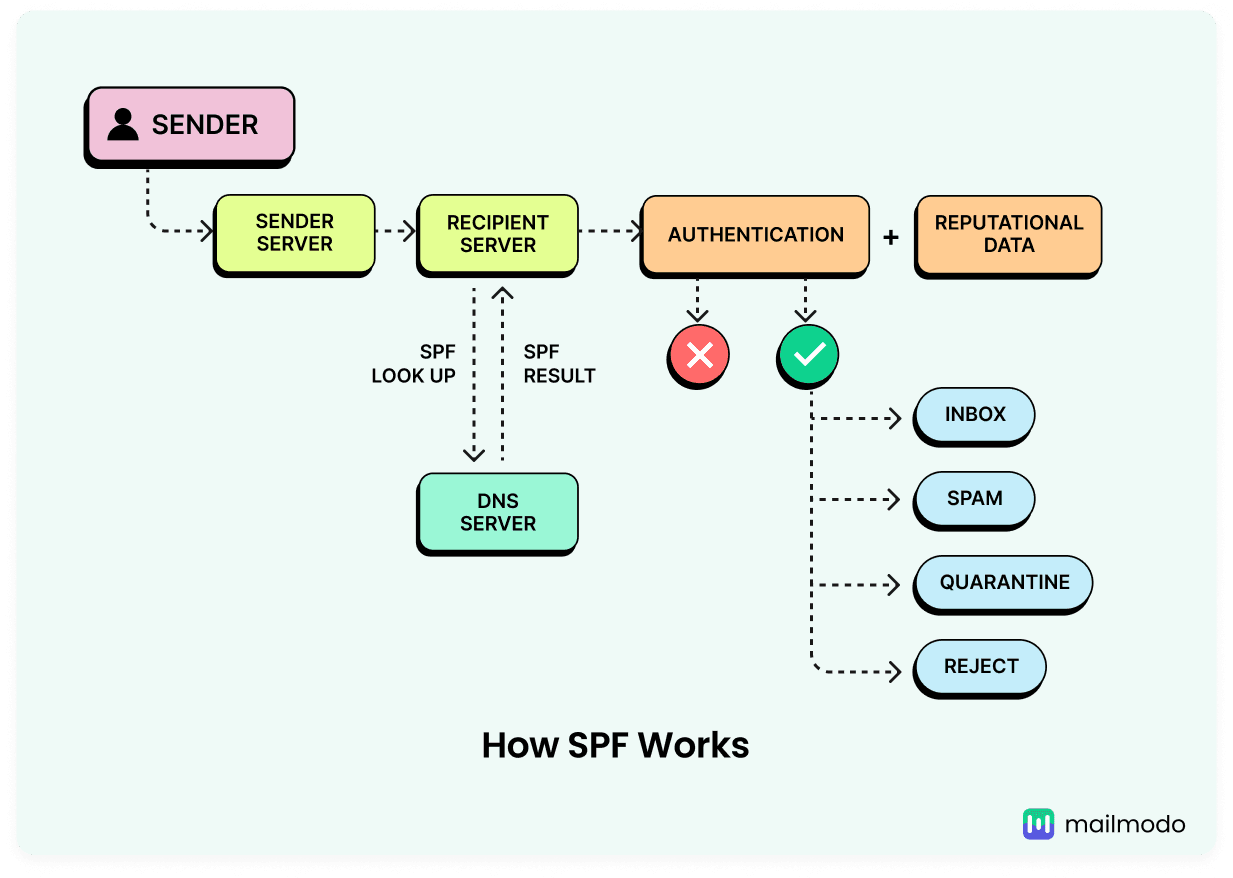
Sender Policy Framework ( SPF) is an email authentication protocol that specifies which email servers are authorized to send emails using your domain. It identifies and prevents email phishing and spoofing.
Take a look at the image below that shows how SPF authentication works. You can also read about SPF checks in detail in our related guide that follows.
💡 Related guide: What Is an SPF Record? How It Works & How to Set It Up
DKIM
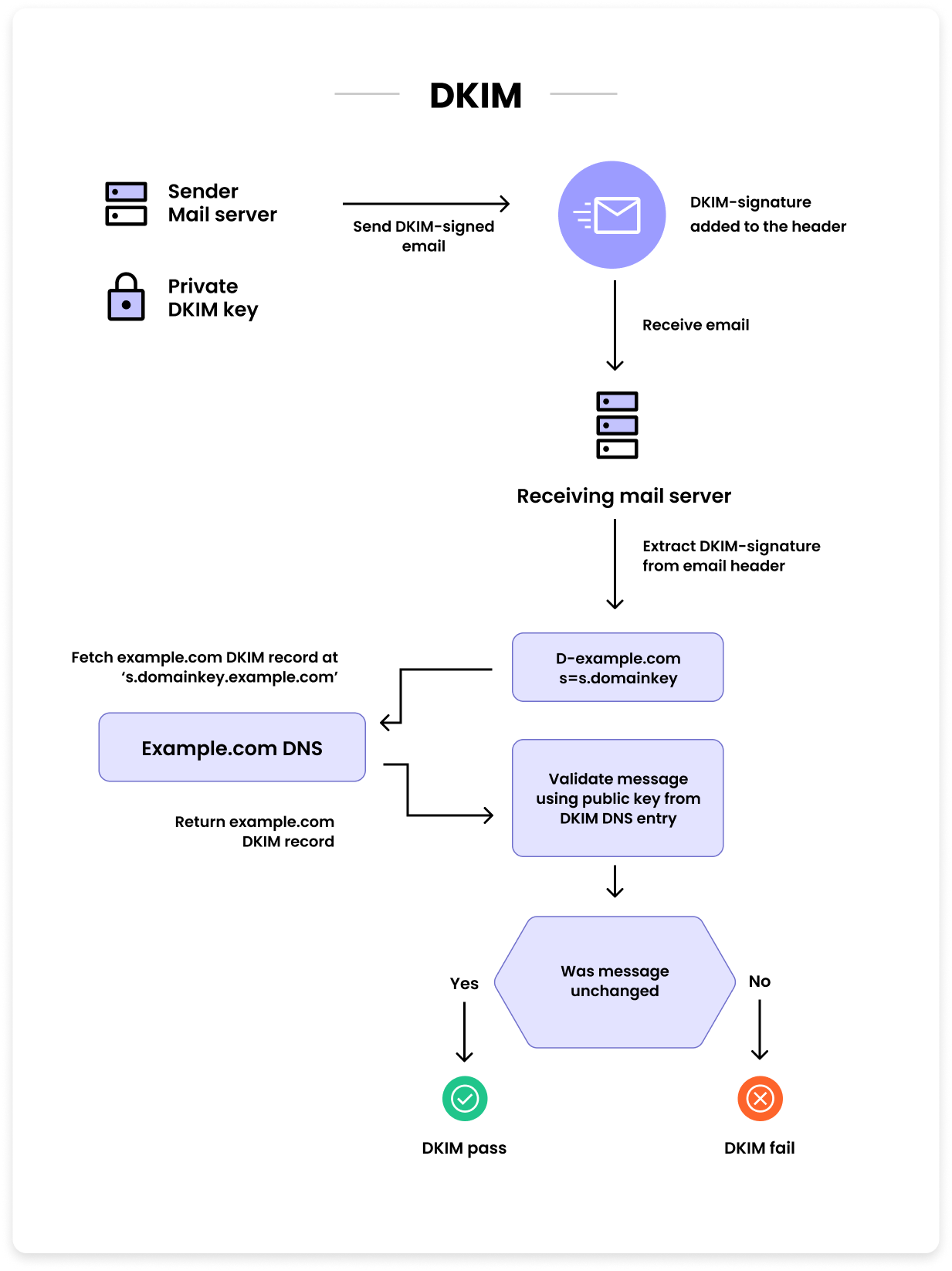
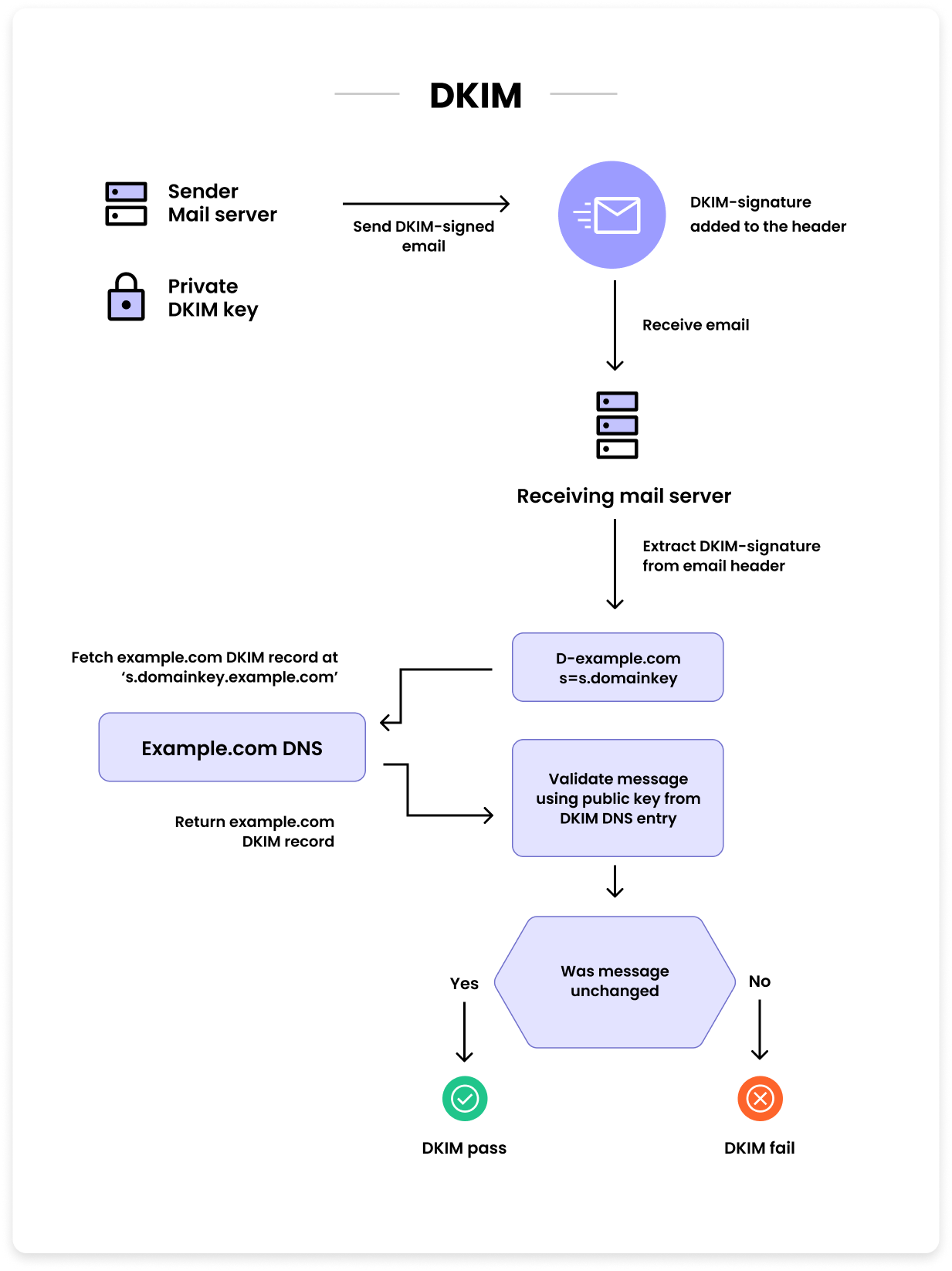
DomainKeys Identified Mail (DKIM) is an email authentication protocol that uses a digital signature to validate the identity of an email sender. It ensures an email was sent from an authorized source and has not been tampered with during transit. DKIM authentication includes a unique message header in the email containing the necessary information for the receiving server to confirm the authenticity of the email.
Take a look at the image below that shows how DKIM record authentication works. You can also read about it in detail in our related guide that follows.
💡 Related guide:
What Is DomainKeys Identified Mail (DKIM) & How Does It Work
DMARC
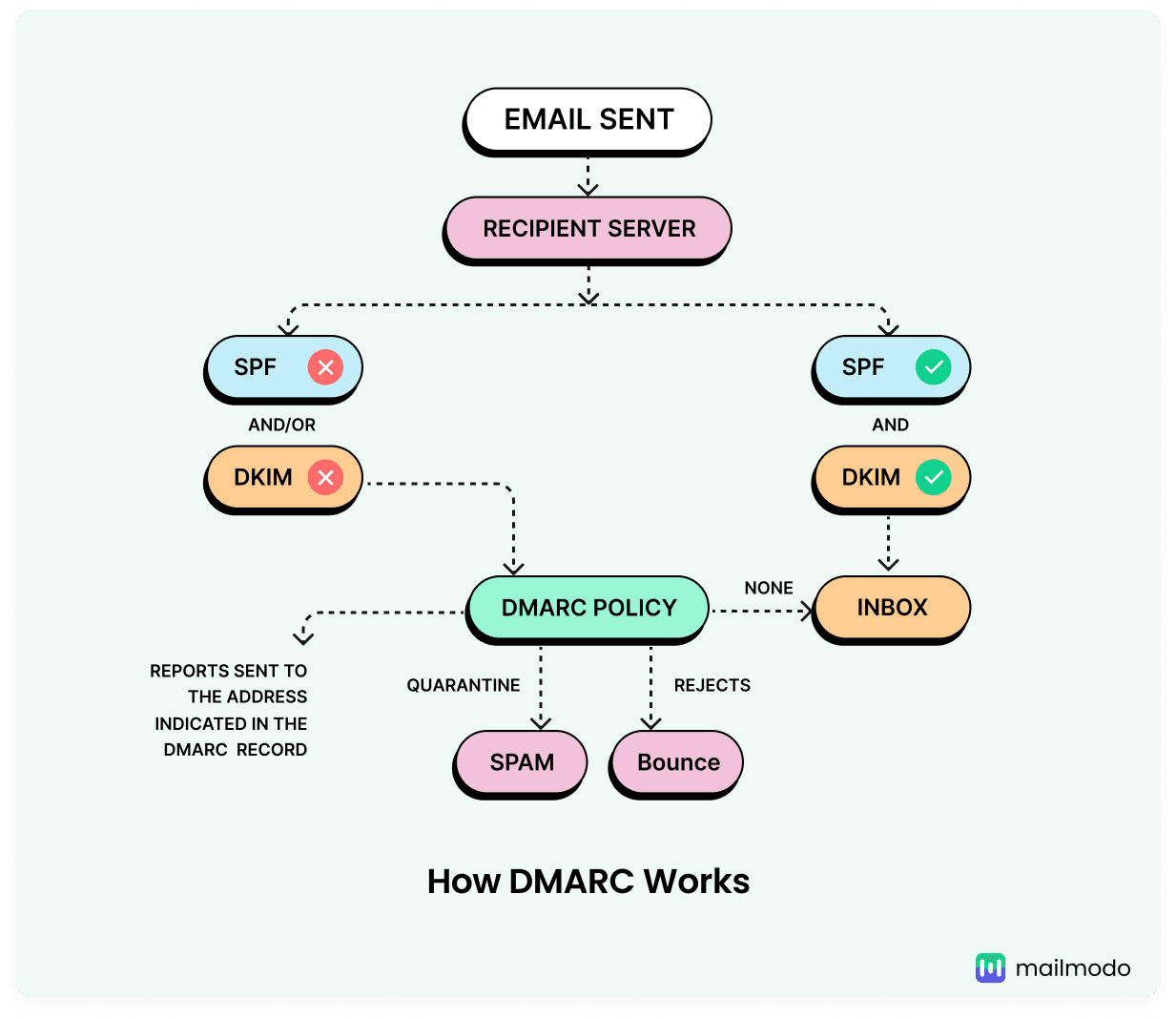
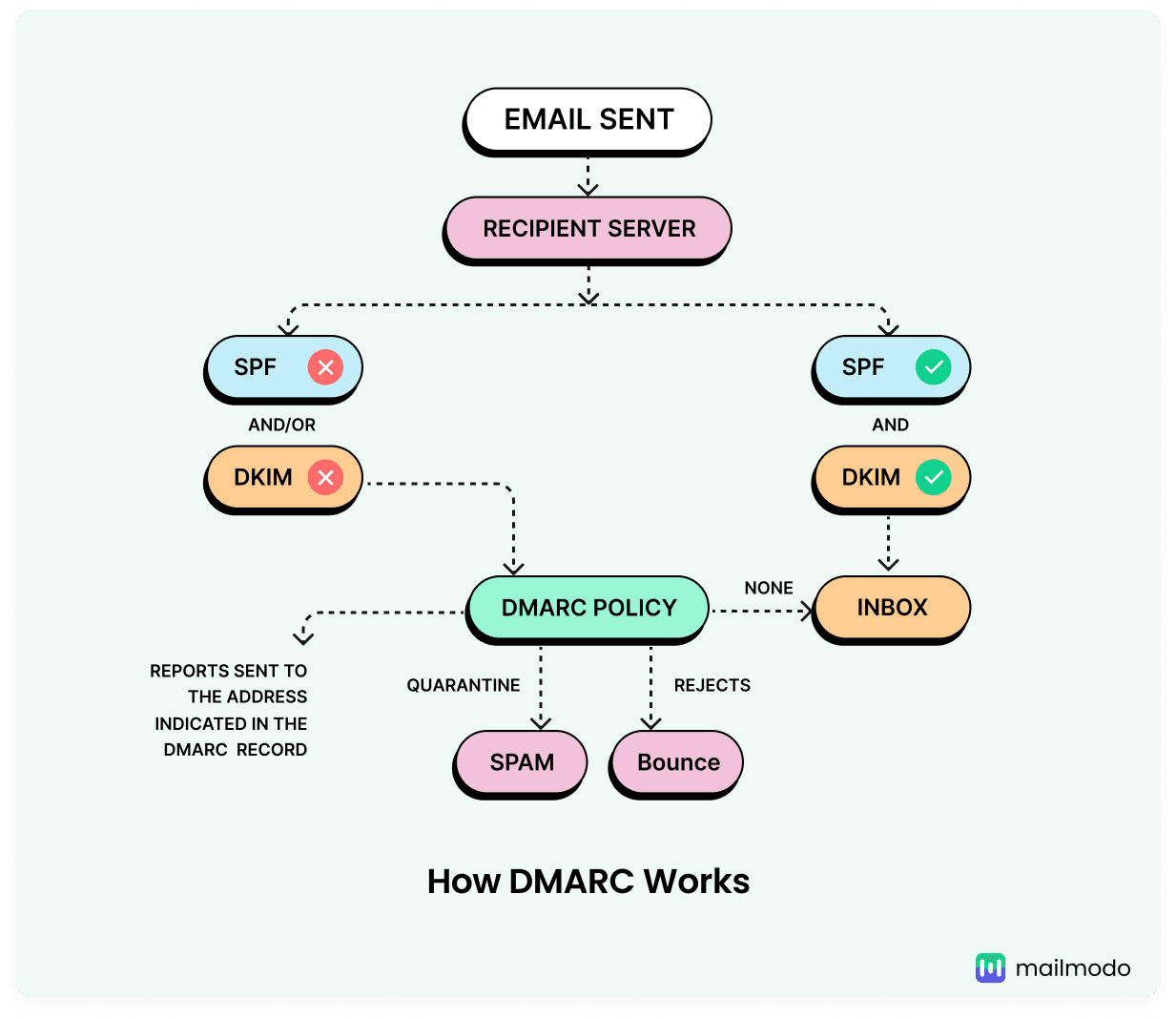
Domain-based Message Authentication, Reporting, and Conformance (DMARC) is an email authentication protocol that uses SPF and DKIM signature checks to perform advanced verification of the received email. It helps domain owners set their email validation policies, instructing servers on how to manage emails that fail SPF and/or DKIM checks.
Take a look at the image below that shows how DMARC works. You can also read about it in detail in our related guide that follows.
💡 Related guide: What Is DMARC and How to Set up DMARC Record?
There's one more added security measure that is closely tied to SPF and DKIM and helps combat phishing and spoofing, and that is BIMI.
BIMI
Brand Indicators for Message Identification (BIMI) is an email standard that allows you to display your brand’s logo in your email messages. This visual representation boosts brand trust and helps email recipients quickly identify valid emails from their favorite brands, improving engagement. BIMI is authenticated by a DMARC policy, which stops billions of email impersonation attacks every year.
💡 Related guide: The BIMI Guide You Need as An Email Marketer
SPF vs DKIM vs DMARC vs BIMI
| Feature |
Purpose |
How It Functions |
Verification Method |
| SPF |
Confirms the sender’s permission to send the email |
Creates a DNS record listing authorized servers |
Receiving server checks the DNS record |
| DKIM |
Confirms the sender’s identity and guards against spoofing |
Attaches a digital signature to the email header using a private key, with the public key stored in DNS |
Receiving server verifies the public key in DNS |
| DMARC |
Defines how emails should be handled |
Establishes a DNS policy for managing emails that fail SPF or DKIM checks |
Receiving server assesses the DNS policy |
| BIMI |
Displays the sender’s logo in the recipient’s inbox |
Creates a DNS record that links to an image file |
Receiving server checks the DNS record |
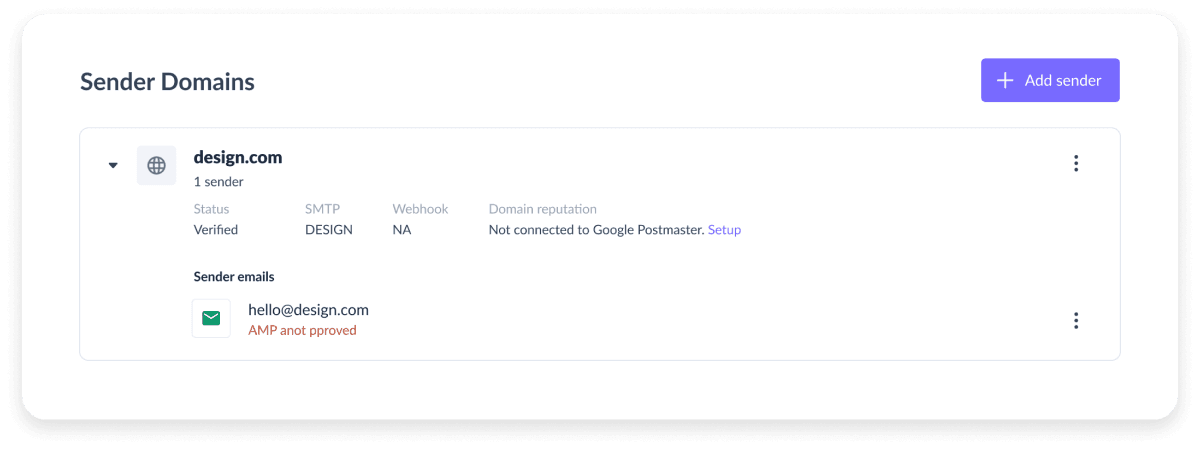
How to set up email authentication in Mailmodo
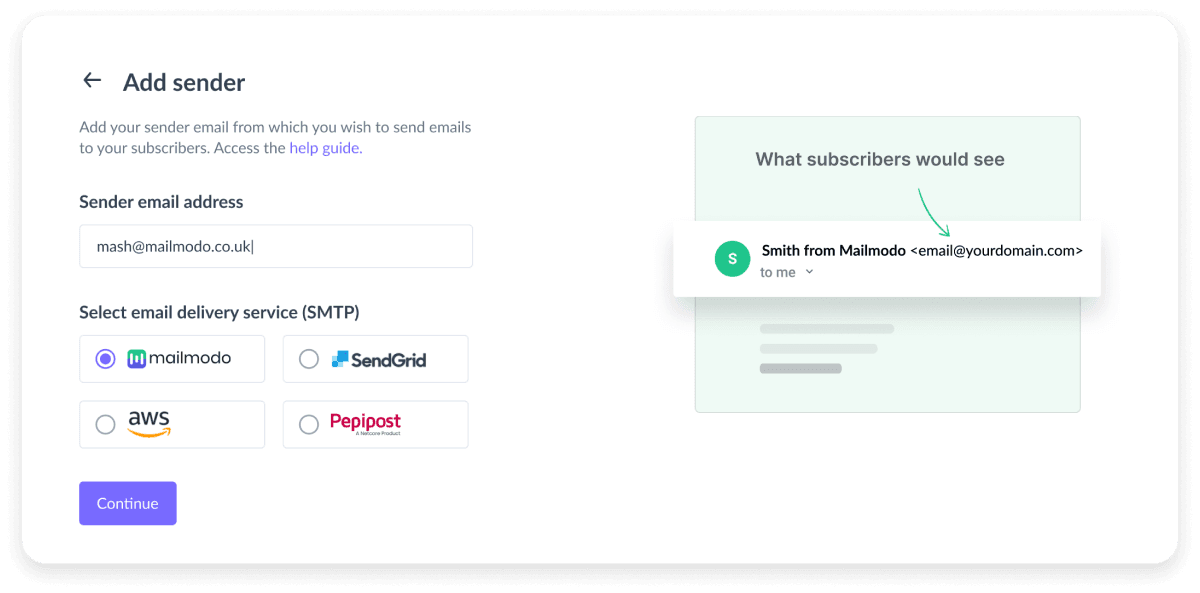
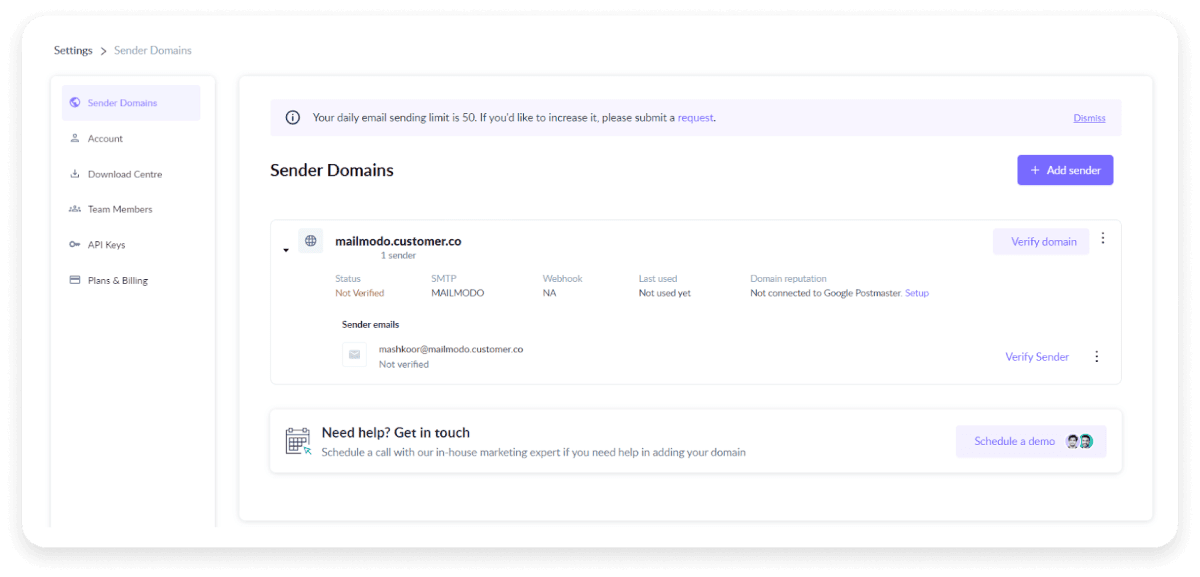
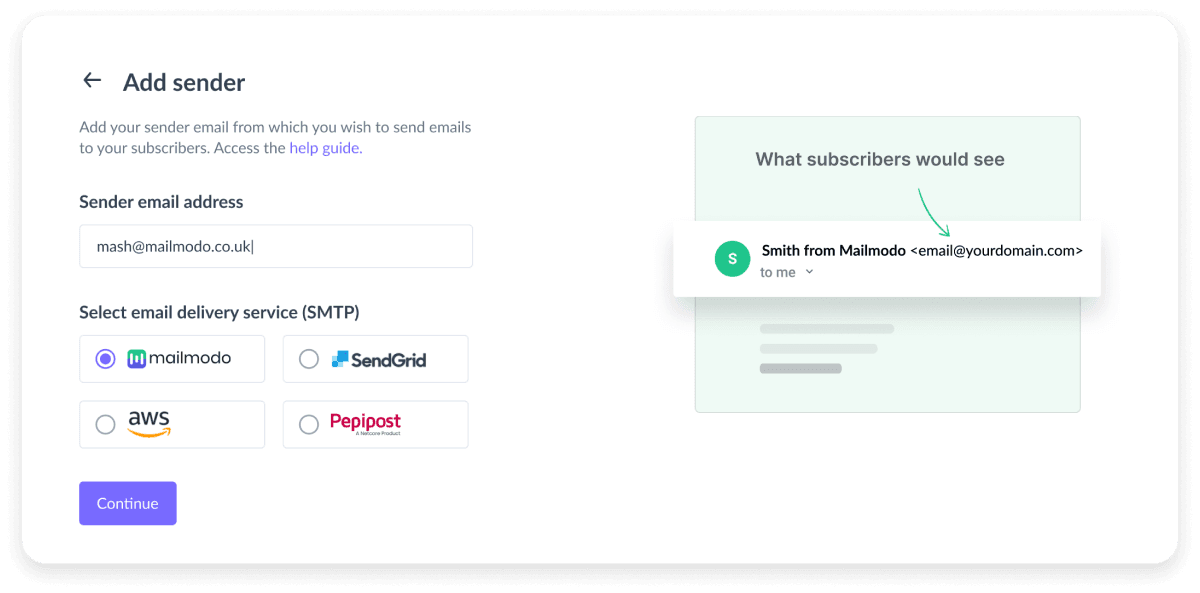
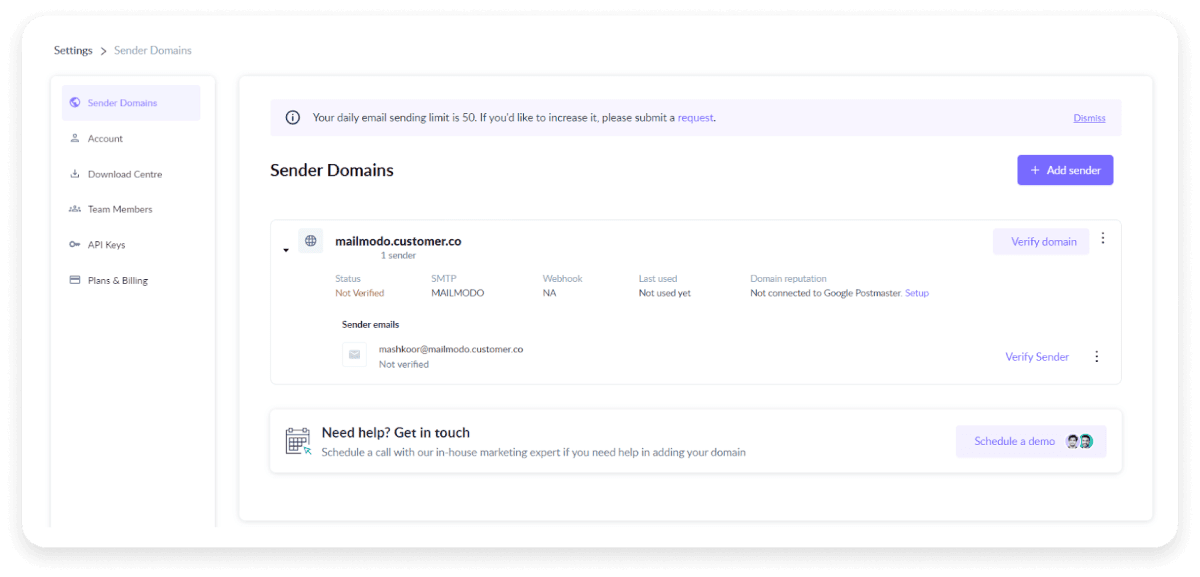
To add a new sender to your Mailmodo account, follow the below steps.
Step 1: Navigate to the Settings section in your Mailmodo account and select “Add sender”. Enter the necessary details.
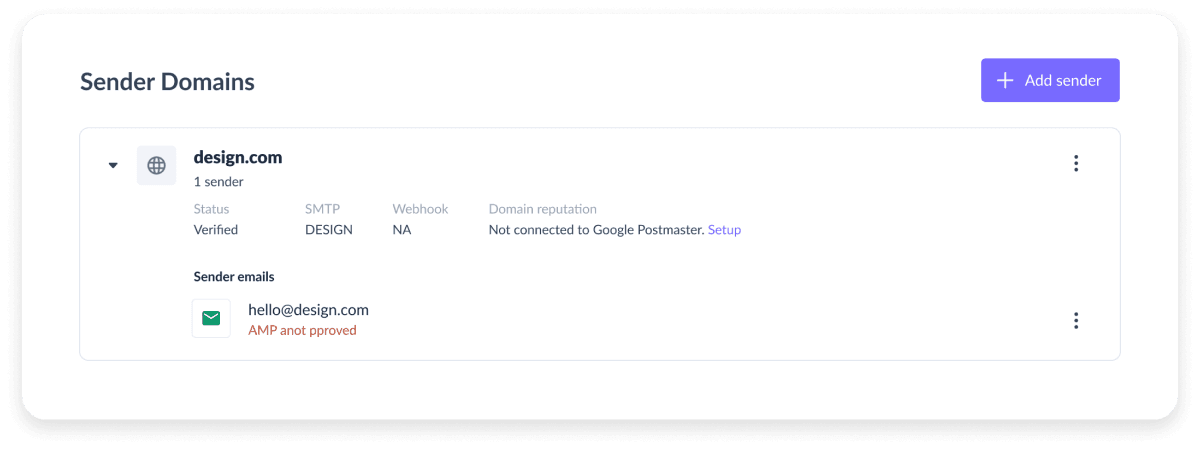
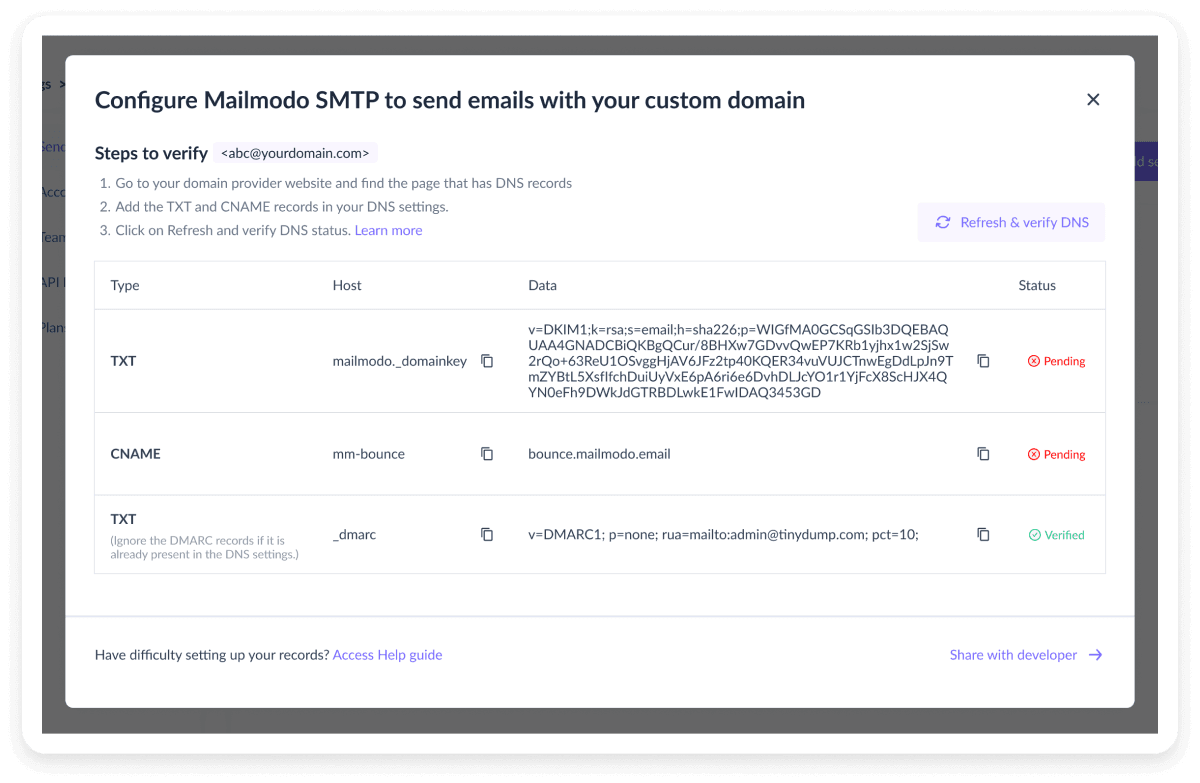
Step 2: Go to the DNS settings of your domain service provider.
Step 3: Create a new TXT record for each authentication protocol.
Step 4: Copy the DKIM, DMARC, and bounce codes provided by Mailmodo and paste them into appropriate fields as values in your domain name system settings.
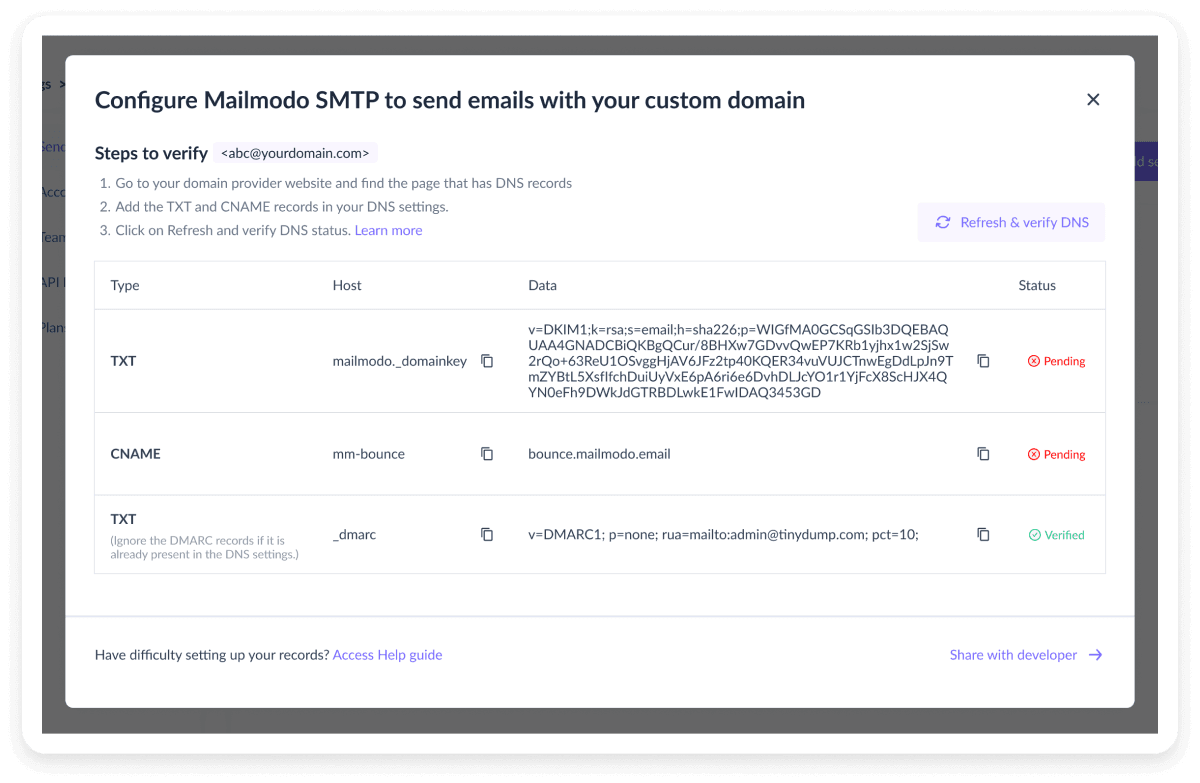
Step 5: Go back to Mailmodo’s sender settings to verify the domain's dns records for the domain.
Conclusion
Email sender authentication protects both senders and receivers from the threats of email fraud. By implementing protocols such as SPF, DKIM, and DMARC, businesses can ensure they receive emails from legitimate sources, improving email deliverability.
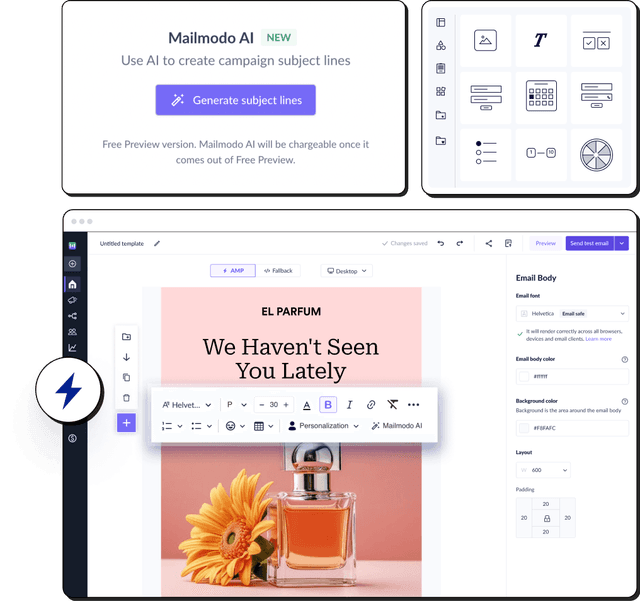
If the process of setting up email authentication seems daunting to you, Mailmodo simplifies it for you. With Mailmodo, you can easily configure authentication protocols and send emails securely to protect your company’s enamel communications.